In the shadows of the net lies a clandestine marketplace referred to as the darknet, where anonymity and secrecy reign splendidly. Darknet markets have emerged as hubs for illicit transactions, providing the entirety from pills and weapons to stolen statistics and counterfeit goods. In this in-depth exploration, we delve into the arena of darknet markets, uncovering their internal workings, popular platforms, and the implications for online protection.
Understanding Darknet Markets
Darknet markets are online platforms that operate within encrypted networks, allowing users to buy and promote goods and services anonymously. These markets leverage technologies consisting of Tor (The Onion Router) to hide users’ identities and places, making it hard for law enforcement agencies to bust illicit sports.
How Darknet Markets Function
1. Anonymity: Darknet markets prioritize user anonymity, frequently requiring customers to get entry to the platform via specialized browsers like Tor. This ensures that transactions stay personal, defending both customers and dealers from detection.
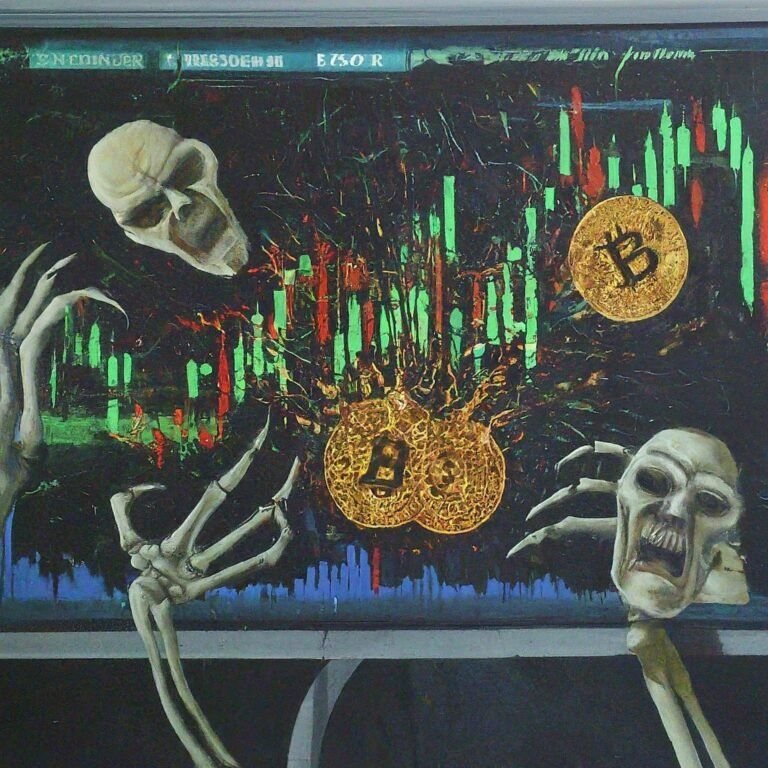
2. Cryptocurrency Transactions: Transactions on darknet markets are conducted using cryptocurrencies along with Bitcoin, Ethereum, or Monero. This decentralized shape of price adds an extra layer of anonymity, making it hard to hint echint atonomic transactions.
3. Vendor Ratings and Reviews: Darknet markets regularly feature a score and evaluation gadget for companies, allowing consumers to assess the reliability and trustworthiness of dealers. Positive scores and critiques can decorate a supplier’s popularity and entice more customers.
4. Escrow Services: To mitigate the danger of fraud, many darknet markets offer escrow offerings, where price rangeshint at are held in escrow until the customer gets and verifies the goods or services. This gives shoppers a layer of protection against potential scams or disputes.
Popular Darknet Markets
1. Silk Road: Silk Road became one of the first and most infamous darknet markets, running from 2011 until its shutdown by law enforcement in 2013. It won notoriety for its huge variety of illicit goods and services, consisting of pills, guns, and counterfeit currency.
2. AlphaBay: AlphaBay once became the biggest darknet market, boasting millions of users and billions of bucks in transactions. It presented a various selection of merchandise, starting from drugs and counterfeit goods to hacking tools and stolen statistics. However, AlphaBay was closed down with the aid of regulation enforcement in 2017.
3. Dream Market: Dream Market changed into a prominent darknet marketplace recognized for its user-friendly interface and strong security features. It operated from 2013 till its closure in 2019, catering to a worldwide person base looking for a huge range of illicit items and services.
4. Empire Market: Empire Market is one of the current leading darknet markets, supplying an extensive selection of merchandise, which includes drugs, digital goods, and counterfeit objects. It has won recognition for its reliability, security, and responsive customer support.
Conclusion
Darknet markets keep thriving no matter ongoing efforts by means of regulation enforcement corporations to close them down. While those structures offer anonymity and comfort for buyers and dealers alike, they also pose good-sized risks, including publicity to scams, malware, and prison repercussions. As such, users have to exercise caution when navigating darknet markets and adhere to strict safety features to shield their identities and financial information. By knowing the internal workings of darknet markets and staying informed about rising threats, users can navigate the darkish internet effectively and responsibly.





